Malware analysis Malicious activity
Por um escritor misterioso
Last updated 17 junho 2024

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

AV-TEST Confirms Skyhigh Security Service Edge Delivers Superior Threat Protection in All Test Categories

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity
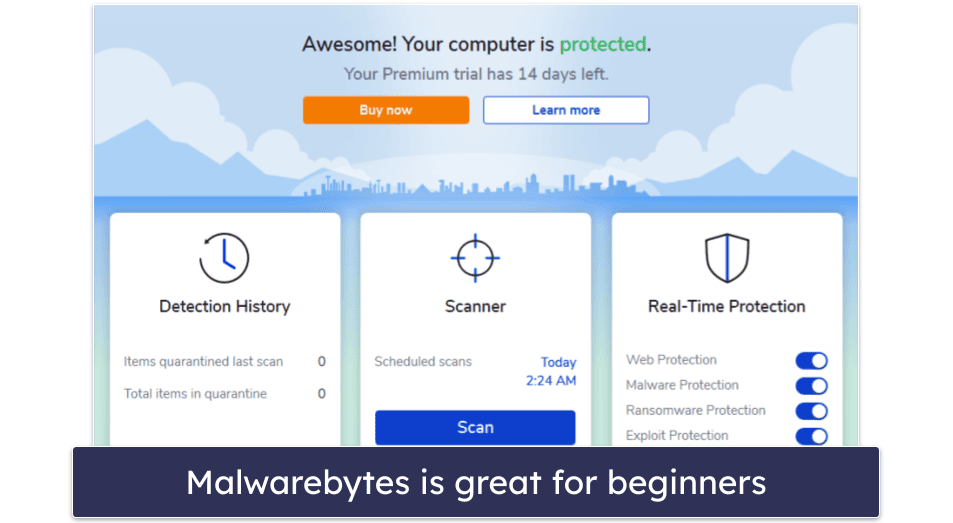
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
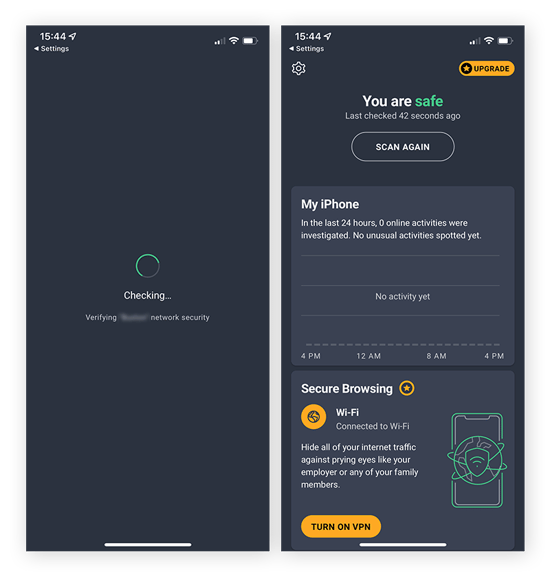
How to Clean an Android or iPhone from Viruses for Free

Malware analysis index.html Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Detail procedure of malware analysis

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks
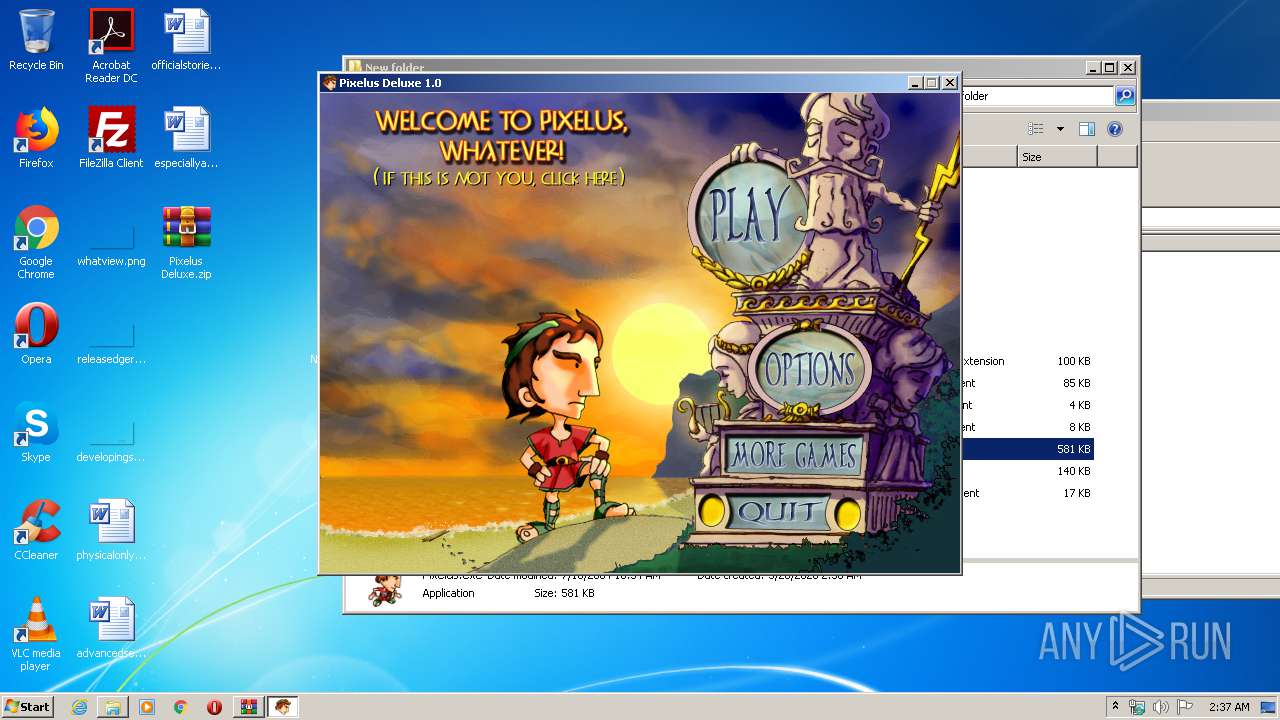
Malware analysis Pixelus Deluxe.zip Malicious activity

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
Recomendado para você
-
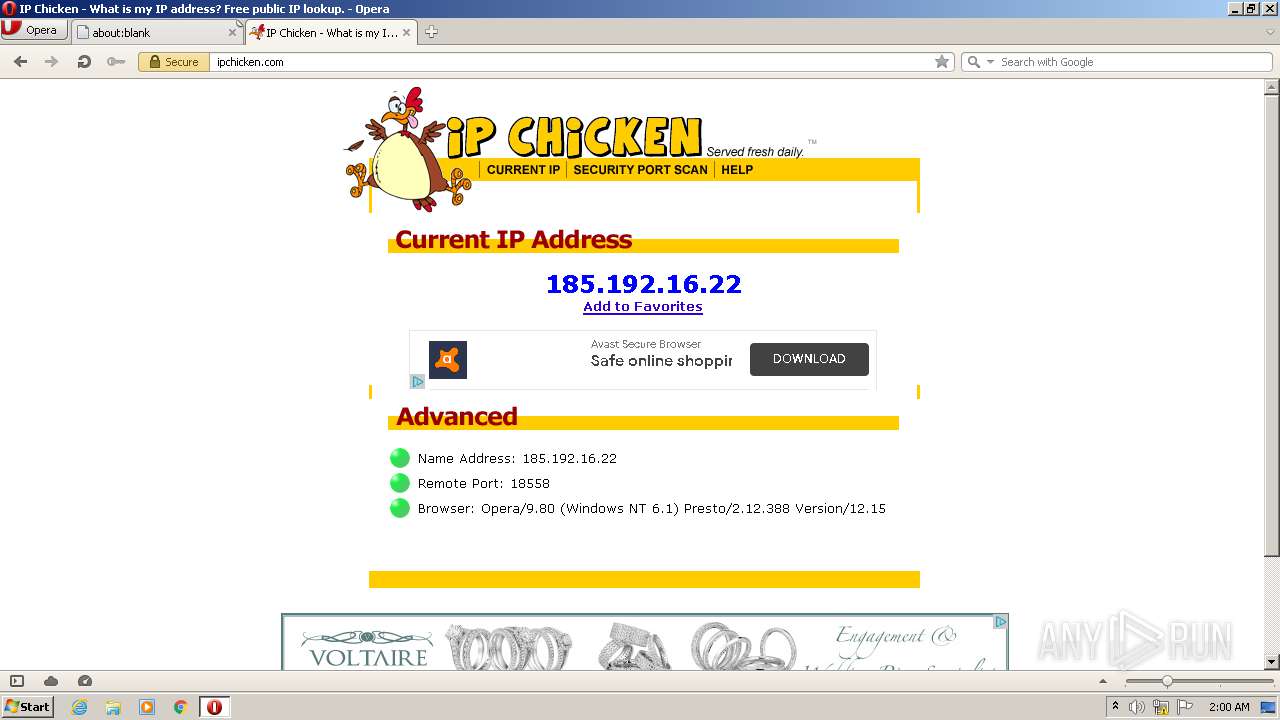
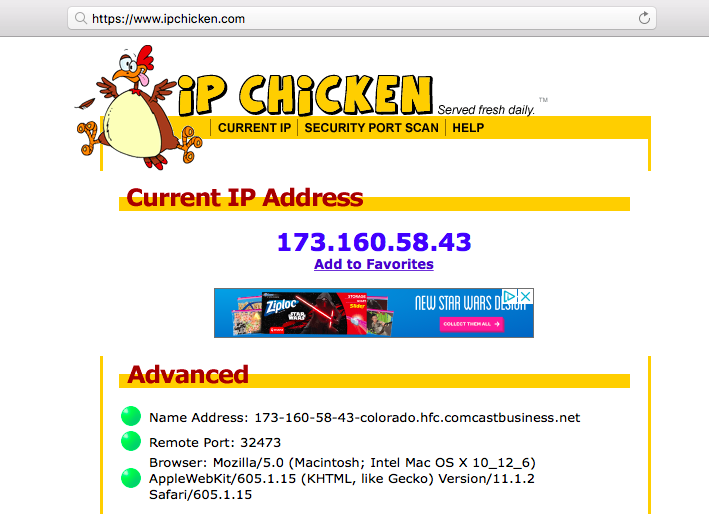
ipchicken.com Traffic Analytics, Ranking Stats & Tech Stack17 junho 2024
-
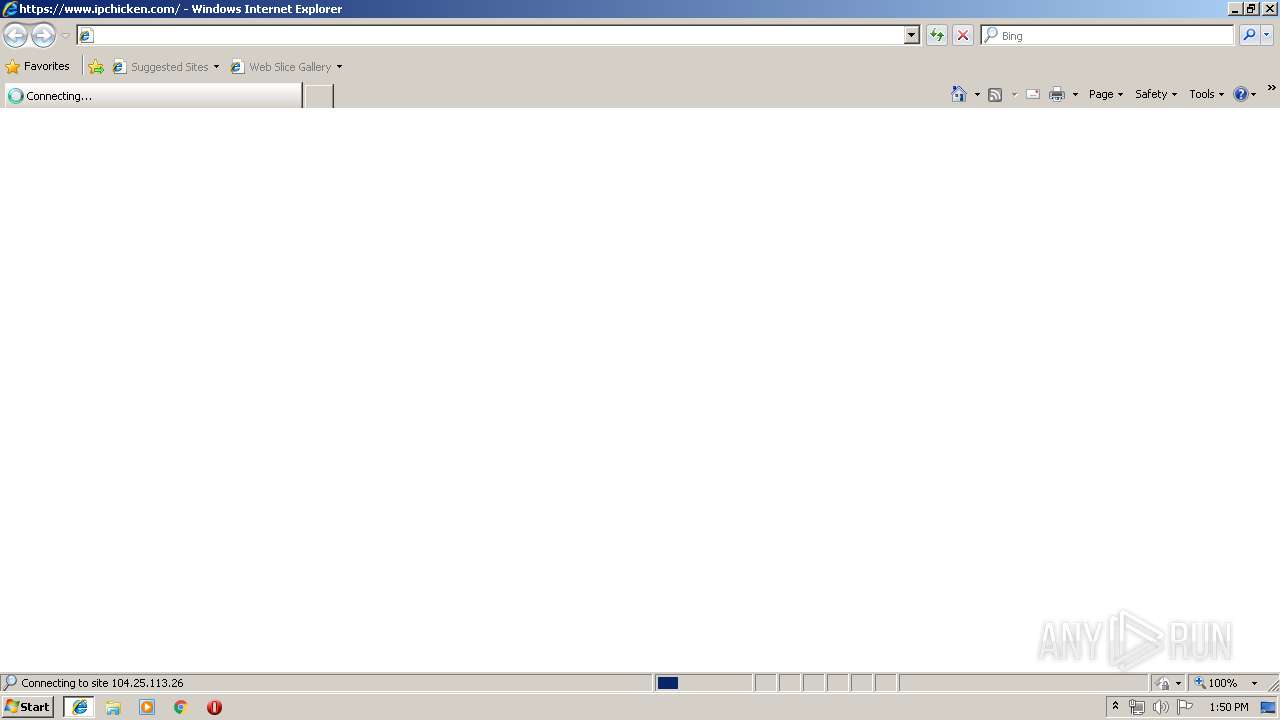 Malware analysis Suspicious activity17 junho 2024
Malware analysis Suspicious activity17 junho 2024 -
 Away Viewing Fix - Dynamic URL Change, WiFi Baby, Compare Baby Monitors 201917 junho 2024
Away Viewing Fix - Dynamic URL Change, WiFi Baby, Compare Baby Monitors 201917 junho 2024 -
![CGNAT: A Complete Guide to Carrier-Grade NAT [2023] — RapidSeedbox](https://www.rapidseedbox.com/wp-content/uploads/CGNAT_03.png) CGNAT: A Complete Guide to Carrier-Grade NAT [2023] — RapidSeedbox17 junho 2024
CGNAT: A Complete Guide to Carrier-Grade NAT [2023] — RapidSeedbox17 junho 2024 -
 What is port scanning and how does it work?17 junho 2024
What is port scanning and how does it work?17 junho 2024 -
 Port Scanner - an overview17 junho 2024
Port Scanner - an overview17 junho 2024 -
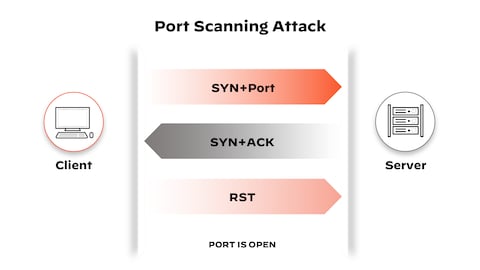 What is a Port Scan? - Palo Alto Networks17 junho 2024
What is a Port Scan? - Palo Alto Networks17 junho 2024 -
Help Center17 junho 2024
-
 Virtualizing pfSense Firewall on Synology DSM Virtual Machine Manager17 junho 2024
Virtualizing pfSense Firewall on Synology DSM Virtual Machine Manager17 junho 2024 -
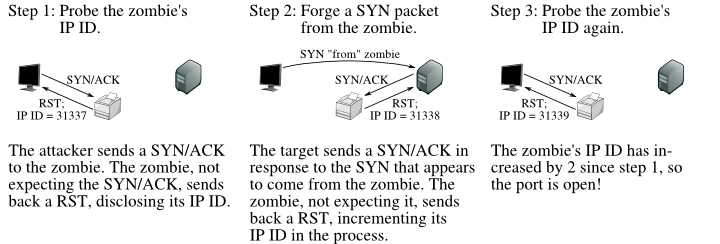 TCP Idle Scan (-sI) Nmap Network Scanning17 junho 2024
TCP Idle Scan (-sI) Nmap Network Scanning17 junho 2024
você pode gostar
-
 Para ator de 'Cobra Kai', série busca a redenção de Johnny Lawrence17 junho 2024
Para ator de 'Cobra Kai', série busca a redenção de Johnny Lawrence17 junho 2024 -
 anime cyberpunk movie still animatrix, small female17 junho 2024
anime cyberpunk movie still animatrix, small female17 junho 2024 -
Jermaine Delos Santos - Staff Writer - PS Legends17 junho 2024
-
 God of War Kratos Mondo 1/6 Scale Figure Unboxing & Review17 junho 2024
God of War Kratos Mondo 1/6 Scale Figure Unboxing & Review17 junho 2024 -
 The Penguin Fan Casting for Who controls Gotham's underworld17 junho 2024
The Penguin Fan Casting for Who controls Gotham's underworld17 junho 2024 -
 William James Sidis: The smartest person yet forgotten by people17 junho 2024
William James Sidis: The smartest person yet forgotten by people17 junho 2024 -
 Corridor 7 - Metacritic17 junho 2024
Corridor 7 - Metacritic17 junho 2024 -
 Os 10 melhores jogadores de futsal do mundo na história17 junho 2024
Os 10 melhores jogadores de futsal do mundo na história17 junho 2024 -
Arena Passione - Sexta 28 de Janeiro de 2022 Arena17 junho 2024
-
 Fullmetal Alchemist: O Conquistador de Shamballa, Dublapédia17 junho 2024
Fullmetal Alchemist: O Conquistador de Shamballa, Dublapédia17 junho 2024